Abhik Dutta: Books Pdf Free Download Portable
Arnav Ghosh, a 32-year-old software engineer and book enthusiast, had always believed that the intersection of technology and mystery held the key to the greatest adventures. His latest obsession? A rare PDF of Cipher Chronicles , a long-out-of-print book by the enigmatic author Elara K. Mistry. The file, downloaded from a obscure Indian forum, boasted cryptic threads claiming the book hide clues to a million-rupee reward.
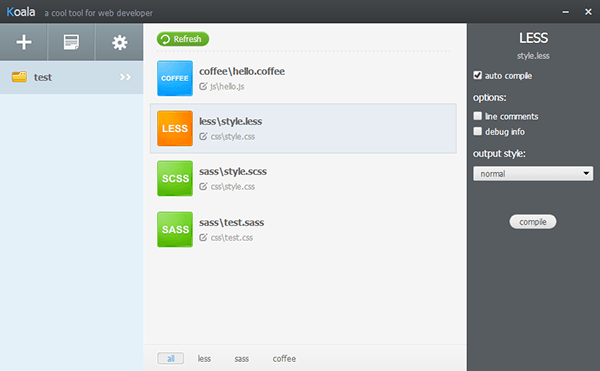
Let me check if there are any specific elements associated with Abhik Dutta's works that I should emulate. His stories often involve police, crime, and suspenseful settings. To mirror that, maybe the protagonist is an ex-cop or a detective, or the story is set in a metropolitan environment with cybercrime. The main conflict could involve a digital artifact that leads to real-world crime. abhik dutta books pdf free download portable
“She’s out there,” Ms. Kapoor said. “Or someone is using her work to control the narrative. Your PDF might not be from 2018.” Arnav Ghosh, a 32-year-old software engineer and book
Make sure the story has the suspense and intrigue typical of Abhik Dutta's style. Maybe include a subplot where the protagonist is racing against time or someone is after them. The resolution should tie back to the digital nature of the problem, perhaps with a clever twist ending that subverts expectations. Mistry
Days later, Arnav handed the data to the cybercrime unit. The lead detective, Ms. Kapoor, thanked him, but revealed a shocking truth: Elara had vanished after her fake death. Her last public IP address showed she’d been in Germany. Yet, the PDF’s metadata Arnav downloaded had a timestamp from last night .
Okay, time to start drafting the story. Let's name the protagonist. Maybe Arnav Ghosh, a book lover and amateur detective. He downloads an old PDF of a book by a reclusive author that's been rumored to contain a hidden message. As he reads, he finds an anagram or a code. He investigates and gets pulled into a mystery involving a cybercriminal network. Along the way, he discovers clues embedded in different PDFs. The twist could be that the real message is a call to action against a company, or that the author faked their death and used the books to pass information.
The message ended with: “Trust no one with the key. EKM.”